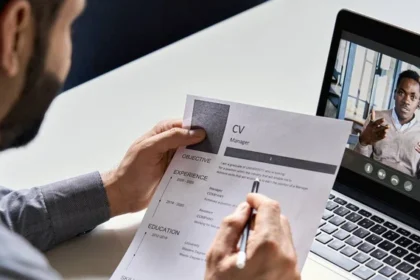
How Technology Is Transforming and Optimizing the Recruitment Process
The Evolution of Modern Recruitment Recruitment has changed dramatically in recent years…
Required Capabilities for Effective and Secure SD-WAN: The Network Leader’s Guide
SD-WAN offers the ability to use available WAN services more effectively and…
Secure SD-WAN Customer Success Stories
Today’s networks are constantly increasing in complexity, and attack surfaces are continuously…
Fortinet Security Operations Solutions Animated Video
Securing your organization against cyber threats must be designed into the very…
Understanding the Security Operations Journey
In today’s cybersecurity landscape, security teams grapple with sophisticated threats that challenge…
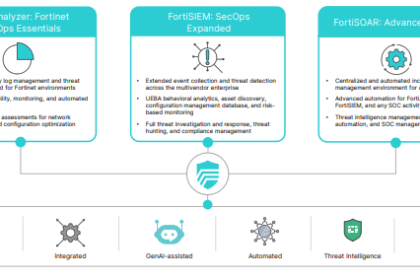
Choose the Fortinet SOC Platform for Unified Threat Response
Security operations teams of all sizes face alert overload, tool-switching inefficiencies, an…
11 Tips for Implementing GenAI into Security Operations
Generative AI (GenAI) offers unprecedented opportunities for enhancing security operations (SecOps). Integrating…
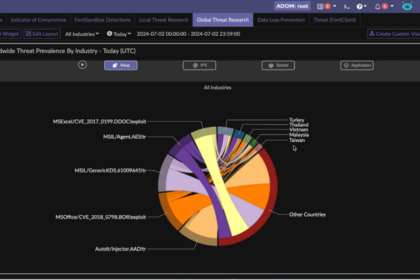
Built-in AI Assistance Streamlines Visibility and Improves Threat Response in Fortinet FortiAnalyzer
In the rapidly evolving world of cybersecurity, the volume, sophistication, and escalating…
Course for Change: How tech companies build resilient supply chains
This report is looking at the strategies employed by resilient tech frontrunners…
Course for Change: How the automotive sector builds resilient supply chains
This report is looking at the strategies employed by resilient automotive frontrunners…